Two-Factor Authentication: Enhancing the Security of Your Mobile Applications
The Importance of Two-Factor Authentication in Today’s Digital Landscape
In an era where mobile applications have become indispensable to our daily routines, the importance of securing these platforms cannot be overstated. Cyber threats are pervasive, with hackers targeting sensitive information ranging from personal details to banking credentials. In response to these escalating risks, two-factor authentication (2FA) stands out as a crucial safeguard for users and businesses alike.
Two-factor authentication bolsters security by requiring two distinct forms of verification before granting access to accounts. This typically entails a combination of something the user knows, such as a password, and something they possess, like a smartphone that generates a unique code or receives a verification text. For instance, after entering a password to log into a banking app, users might receive a text with a one-time code that they must enter to finalize the login process. This dual-layer approach significantly mitigates the risks of unauthorized access, especially in a world where passwords can easily be stolen through phishing scams or data breaches.
Key Benefits of Two-Factor Authentication
- Enhanced Security: Even if a cybercriminal obtains a user’s password, the additional layer of verification acts as a critical barrier against unauthorized access. According to a study conducted by Google, 2FA can block up to 99.9% of automated account hijacking attempts.
- Increased User Trust: Users are becoming increasingly cautious about sharing their information. By providing enhanced security measures like 2FA, businesses communicate a commitment to user safety, fostering greater trust and customer loyalty.
- Compliance: In the United States, many organizations are required to adhere to industry regulations that demand robust authentication mechanisms. For example, the Financial Industry Regulatory Authority (FINRA) mandates that financial firms implement 2FA to protect sensitive financial data, making compliance a significant driver for adopting such technologies.
As mobile applications evolve and become more integrated into the fabric of our lives, the incorporation of 2FA is shifting from being an optional feature to a fundamental necessity. By leveraging this method, developers enhance the application’s defenses against invasive threats. Notably, adopting 2FA can also play a pivotal role in reducing hacking incidents, a serious concern reflected in reports indicating that 81% of data breaches are linked to stolen or weak passwords.
Implementing 2FA is a step every individual and business should consider to fortify their cybersecurity posture. In a digital age characterized by constant threats, understanding and utilizing two-factor authentication can dramatically reshape how we perceive and prioritize app security, providing users with the peace of mind they deserve amidst growing uncertainties.
DIVE DEEPER: Click here for insights on effective usability testing

Understanding How Two-Factor Authentication Works
At its core, two-factor authentication (2FA) is designed to add an extra layer of security to the standard password-only approach we are all familiar with. The mechanics of 2FA involve two steps—a username and password followed by a second verification step that can either be something you have or something you are. This might be a fingerprint scan, a face recognition on your mobile device, or a physical security key that plugs into your device. The essence of 2FA is to ensure that even if one factor (like a password) is compromised, unauthorized access can still be prevented.
Consumers today have widely embraced mobile applications ranging from social media to banking, with many storing sensitive personal information. A recent survey from the Pew Research Center indicates that 75% of Americans feel concerned about their online safety, emphasizing the urgent need for robust security solutions. With a constantly evolving landscape of cyber threats, it becomes paramount for developers and organizations to integrate 2FA into their mobile apps.
How 2FA Enhances Security for Mobile Applications
Integrating 2FA into a mobile application provides several layers of security that are vital for today’s digital users. The adoption of this technology can be a game changer for maintaining user integrity and safety. Here are some specific ways 2FA enhances security in mobile applications:
- Reduction of Identity Theft: With 2FA, even if a hacker successfully acquires a user’s password, they are unable to access the account without the second authentication factor.
- Real-time Alerts: Many 2FA systems provide immediate notifications regarding login attempts, allowing users to respond swiftly to potential security threats.
- Adaptability: 2FA methods can adapt to the potential threat at hand. For instance, geolocation can be used to determine if a login attempt is made from an unfamiliar IP address, triggering a 2FA process.
This multi-layered approach is particularly crucial in today’s climate where hacking attempts are frequent, and consumers are increasingly aware of their digital footprint. The fact that up to 90% of data breaches are caused by human error, notably related to password management, emphasizes the importance of integrating solutions like 2FA.
As various industries adopt more rigorous security protocols, 2FA stands out as a fundamental requirement. It significantly lowers the likelihood of successful attacks on mobile applications while providing users with the assurance that their data is safe. This growing focus on robust security reinforces the need for both businesses and users to prioritize the implementation of strong, effective authentication measures. By understanding and utilizing 2FA, users can navigate the digital landscape with greater confidence.
| Advantage | Importance |
|---|---|
| Increased Security | Two-factor authentication (2FA) adds an extra layer of protection by requiring not just a password but also an additional verification method. |
| Fraud Prevention | By implementing 2FA, mobile applications significantly reduce the risk of unauthorized access, thus safeguarding sensitive information. |
| Ease of Use | Many users find 2FA to be a simple yet effective measure to secure their mobile applications while maintaining accessibility. |
As the digital landscape evolves, the mantra remains that prevention is always better than cure. Employing 2FA is not just a trend; it’s a necessity that every organization must consider to enhance security protocols for mobile applications. The ease with which users can access their accounts should never compromise the integrity of their data. Hence, reinforcing security measures like two-factor authentication redefines the balance between convenience and protection. By opting for 2FA, users not only bolster their account defenses but also foster an environment resistant to breaches and cyberattacks, making it indispensable for any mobile application today. This step forward holds the promise of not just securing personal data but also reinforcing user trust and loyalty—a critical aspect in a competitive app market.
DISCOVER MORE: Click here for insights on effective usability testing
Implementing Two-Factor Authentication in Your Mobile Applications
For developers and businesses aiming to enhance the security of their mobile applications, integrating two-factor authentication (2FA) isn’t just a matter of best practice; it’s becoming a necessity. As the threat landscape grows more sophisticated, end-users are increasingly looking for assurances that their data is adequately protected. Implementing 2FA can not only elevate security but also enhance the overall trust between users and service providers.
Choosing the Right 2FA Methods
Effective implementation of 2FA involves selecting suitable authentication methods that resonate with user preferences and technological constraints. Popular 2FA methods include:
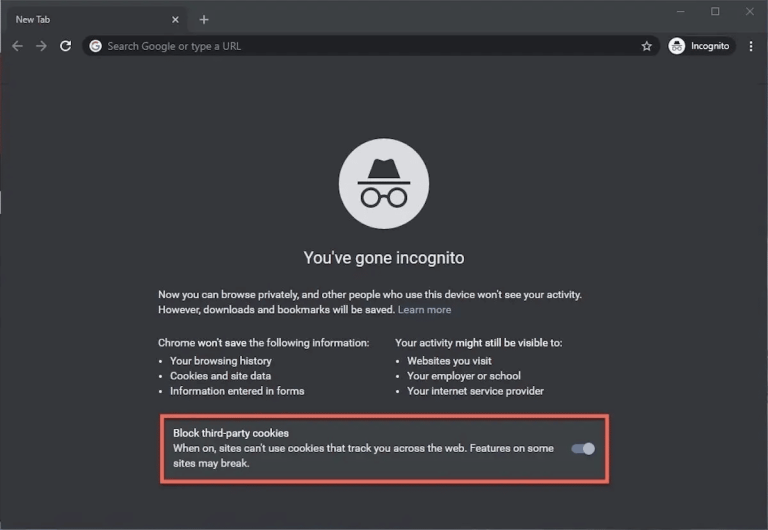
- SMS-Based Verification: A widely adopted method where a one-time code is sent via text message. However, while convenient, it’s vulnerable to SIM swapping attacks and interception.
- Authenticator Apps: Applications like Google Authenticator or Authy generate time-sensitive numeric codes. These are generally more secure than SMS, as they do not rely on cellular networks.
- Biometric Authentication: Features such as fingerprint scans or face ID add a layer of security that is both user-friendly and difficult to replicate.
- Push Notifications: Users receive a prompt on their registered devices, allowing them to approve or deny login attempts in real-time.
Businesses need to weigh the benefits and drawbacks of each method thoroughly, ensuring user-friendliness doesn’t overshadow security measures. Choices may also depend on the sensitivity of the data being handled, with financial applications demanding a far more rigorous approach than casual social media platforms.
User Education and Engagement
Once 2FA is implemented, user education becomes a cornerstone of successful adoption. Studies suggest that up to 70% of users may initially opt out of 2FA due to a perceived inconvenience. Engaging users through informative tutorials or onboarding sessions can bridge this gap. Explaining how 2FA works and the specific risks involved in not using it can motivate users to embrace this additional security measure. Offering rewards or incentives for enabling 2FA can also boost participation rates.
The Business Case for 2FA
The financial benefits of implementing 2FA cannot be overstated. A single data breach can cost companies millions of dollars in remediation efforts, legal fees, and reputational damage. The Ponemon Institute estimates that the average cost of a data breach stands at around $4.24 million in the U.S. alone. By proactively adopting robust security measures like 2FA, companies may save significant amounts of money and preserve customer loyalty in the long term. Furthermore, regulatory compliance in sectors such as healthcare and finance increasingly mandates stronger authentication measures, making 2FA a strategic necessity.
Incorporating 2FA into mobile applications is not just a technical enhancement; it’s a commitment to safeguarding user information and enhancing trust. With an array of methods available, careful selection and implementation can provide formidable defenses against unauthorized access while simultaneously educating and engaging users to actively participate in their own digital security. As awareness of cyber threats grows, integrating strong security measures like 2FA will remain essential for the survival and success of mobile applications in the competitive digital landscape.
DISCOVER MORE: Click here to learn about effective usability testing
Conclusion: The Imperative Role of Two-Factor Authentication
As the digital landscape continues to evolve, two-factor authentication (2FA) emerges as a vital line of defense for mobile applications against increasingly complex cyber threats. The imperative to protect personal and sensitive data cannot be overstated; every breach carries the potential for significant financial and reputational damage. By integrating 2FA, businesses not only safeguard their users but also reinforce their brand’s integrity in an era where trust is paramount.
Choosing the right authentication methods, whether through SMS, authenticator apps, biometrics, or push notifications, is crucial in catering to user preferences while ensuring robust security. Beyond technical implementation, engaging users through educational initiatives is essential to increase adoption rates of these technologies. With studies indicating that a considerable proportion of users may resist using additional security features due to perceived inconvenience, it becomes critical to bridge the knowledge gap and nurture a security-aware culture.
Furthermore, the financial implications of data breaches reinforce the strategic necessity of implementing two-factor authentication. With the average cost of a breach trending upwards, organizations that proactively invest in security measures like 2FA stand to save not only their resources but also their customer relationships. In conclusion, as data security concerns escalate, embracing two-factor authentication is not merely an option; it is an essential strategy for the survival and flourishing of mobile applications in today’s interconnected world. By prioritizing 2FA, businesses can provide enhanced security while building a foundation of trust and loyalty with their users, ultimately leading to a more secure digital ecosystem.
Beatriz Johnson is a seasoned tech writer and digital tools expert with a passion for simplifying the complexities of technology and mobile applications. With over a decade of experience in the tech industry, she specializes in topics like productivity apps, software reviews, and emerging digital trends. Through her work, Beatriz empowers readers to make informed technology choices and stay ahead in the ever-changing world of apps and innovation.